How to Harden AWS security group outbound rules with VPC Flow Logs, Athena, and AWS Bedrock
22/04/2026
240
When cloud security teams talk about network exposure, the conversation usually starts with inbound traffic. But AWS Security Group outbound rules deserve just as much attention, because broad egress permissions can create a serious blind spot in many AWS environments. Which ports are open, which services are internet-facing, and which entry points need tighter control are important questions, but they are only half the story.
Outbound traffic matters just as much. In many AWS environments, workloads still run with broad outbound permissions because it is the fastest way to get applications working. That may feel harmless at first, especially in development or early deployment stages. But over time, unrestricted egress makes it harder to enforce least privilege, harder to investigate suspicious behavior, and harder to contain damage if a system is ever compromised. When workloads can initiate connections to almost anywhere, the business loses a valuable layer of control.
That is why hardening AWS Security Group outbound rules deserves more attention in modern cloud architecture. The goal is not to lock everything down blindly. It is to replace broad, default access with precise, evidence-based rules. In practice, that means understanding what your workloads actually connect to, identifying which destinations and ports are truly required, and then building outbound rules that reflect real application behavior.
With AWS VPC Flow Logs and Athena, teams can analyze that traffic in a structured way. With AWS Bedrock, they can speed up the investigation workflow by turning natural-language questions into useful query patterns. This article walks through that approach and shows how to move from “allow everything” to a more disciplined least-privilege model for outbound network access.
A note on how Security Groups handle traffic state
Before writing egress rules, it helps to understand one foundational behavior behind AWS Security Group outbound rules: AWS Security Groups are stateful. This means that if an outbound connection is permitted by an egress rule, the return traffic for that connection is automatically allowed back in. You do not need a matching inbound rule to permit the response packets. The reverse is also true: inbound rules that allow a connection automatically permit the corresponding outbound response.
This is different from stateless controls like Network ACLs (NACLs), where you must explicitly permit traffic in both directions.
For egress hardening, statefulness has a practical implication. When you restrict AWS Security Group outbound rules, you are controlling which connections your workload can initiate, not which response packets can return. A workload with no outbound rules, or a deny-all egress configuration, cannot initiate any external connections, even if broad inbound rules are in place. That is an important distinction when reasoning about what tight egress rules actually protect against.
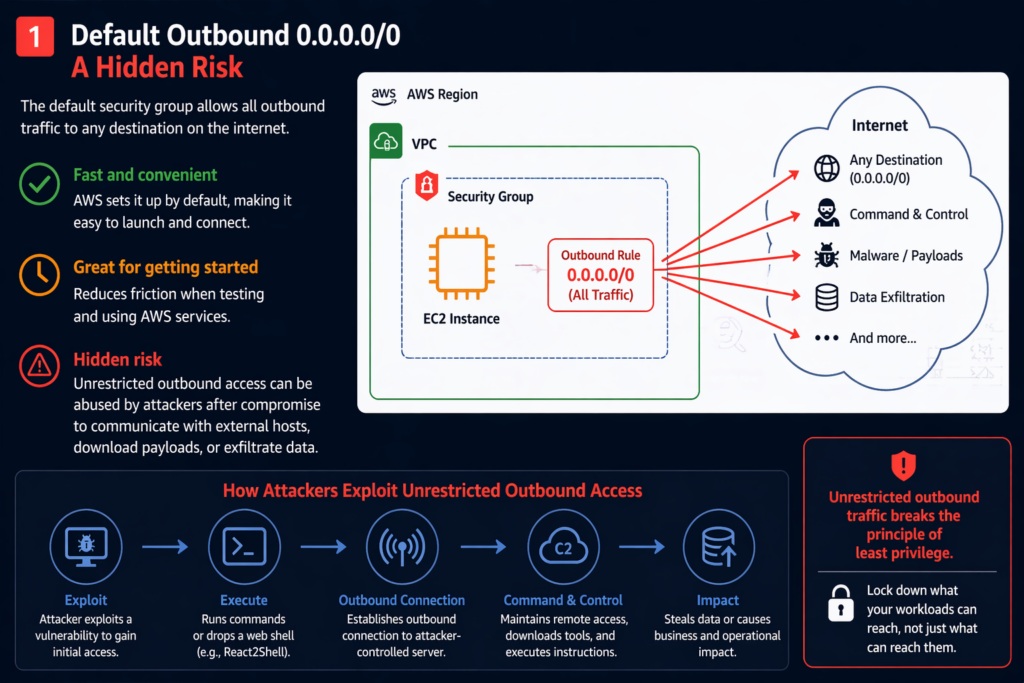
Why default outbound access becomes a security problem
AWS security group outbound rules are popular for a reason. They reduce friction.
When a new EC2 instance launches, it often needs to reach package repositories, third-party APIs, update services, monitoring platforms, or identity providers. Allowing all outbound traffic makes those dependencies work without extra planning. For busy teams, especially in fast-moving delivery environments, that convenience is hard to resist.
The problem starts when temporary convenience becomes permanent architecture.
If a workload can connect to any destination, that permission becomes part of the attack surface. A compromised instance does not just pose a local risk. It may also be able to call out to external infrastructure, download additional payloads, maintain remote control channels, or send data to unauthorized destinations. In other words, unrestricted egress makes post-compromise activity easier.
This is where the principle of least privilege becomes especially important.
Least privilege is often discussed in terms of IAM roles, user permissions, or inbound network exposure. But the same logic applies to outbound communication. A workload should only be able to connect to the destinations and services it genuinely needs. Anything broader than that increases exposure without creating real business value.
For many teams, this is the real turning point. Outbound rules stop being treated as a default setting and start being treated as a deliberate security control.
Why outbound hardening should be data-driven
One reason egress hardening gets delayed is that it seems risky to change.
Teams worry that if they tighten outbound rules, something critical will break. That concern is valid. Most production systems depend on more external services than people remember. APIs, update endpoints, logging backends, container registries, DNS paths, SaaS integrations, and internal service-to-service calls can all be affected.
That is why outbound hardening should not start with guesswork.
Instead, it should start with evidence.
A practical approach usually begins with two activities running in parallel. First, review the system architecture, documentation, and current configuration. Second, analyze actual network behavior. Documentation tells you what the application is supposed to use. Traffic analysis tells you what it is really using. The gap between those two views is often where the most useful security insights appear.
This data-driven approach changes the conversation. Rather than asking, “What might this server need?” you can ask, “What does this server actually connect to, how often, and why?”
That is a much stronger foundation for writing precise Security Group rules.
A practical workflow for restricting outbound Security Group rules
Moving to least-privilege outbound access does not have to be complicated. In most environments, the process can be broken into four steps.
Identify necessary outbound traffic
Start by mapping what the workload truly needs to reach.
That includes external APIs, software repositories, monitoring endpoints, authentication services, payment gateways, partner platforms, and internal dependencies that cross subnets or environments. At this stage, the goal is discovery, not enforcement.
Write narrow outbound rules
Once the required traffic is understood, write rules that are as specific as possible.
That usually means allowing only the destination ports, protocols, and IP ranges or CIDRs that are needed. For example, if a workload only needs outbound HTTPS access to a known destination range, there is no reason to keep a broad egress rule open to all traffic.
Test in lower environments first
Before making the change in production, validate it in DEV or STG.
This is where hidden dependencies show up. Teams often discover overlooked services only after restrictions are applied. That is not a sign the process failed. It is a sign the process is working. Testing exposes assumptions before they become outages.
Apply in production and maintain continuously
Production rollout should be followed by monitoring, review, and cleanup.
Outbound policies are not static. Applications evolve, vendors change endpoints, integrations are added, and old dependencies disappear. A strong outbound security posture depends on periodic review, not just a one-time rule rewrite.
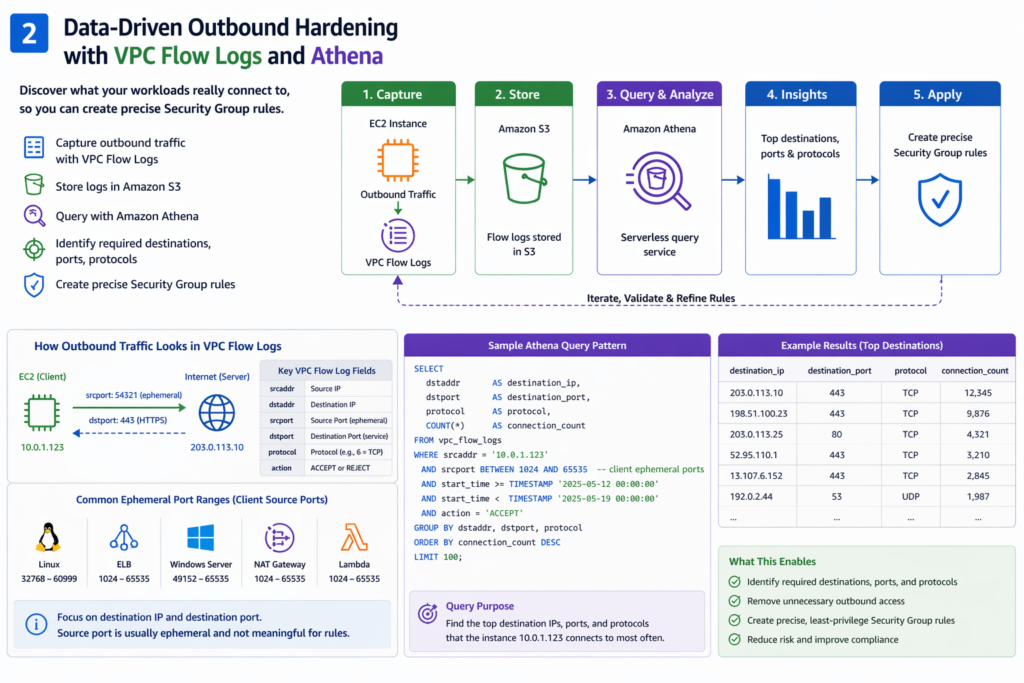
Using VPC Flow Logs to understand real outbound behavior
To harden outbound rules effectively, you need visibility into what your workloads are doing now.
AWS VPC Flow Logs provide that visibility. They capture metadata about network traffic flowing through your VPC and make it possible to analyze communication patterns over time. For outbound analysis, several fields are especially useful: source address, destination address, source port, destination port, protocol, and action. Those fields help you identify which workload initiated the traffic, where it connected, how it connected, and whether the connection was accepted or rejected.
This is where many teams start to see outbound traffic more clearly.
Instead of reasoning only from architecture diagrams or memory, they can inspect real destinations and real traffic patterns. That makes it much easier to separate essential connections from broad, unmanaged access.
The source port vs. destination port mistake
One of the most common mistakes in outbound analysis is focusing on the wrong side of the connection.
In a typical client-server model, the workload initiating the connection uses a temporary source port, often called an ephemeral port. The destination, on the other hand, usually listens on a well-known service port such as 443 for HTTPS. If you confuse the client’s ephemeral source port with the server’s service port, you can end up writing inaccurate outbound rules.
This distinction matters a lot when analyzing EC2 egress behavior.
If an instance is connecting out to a public service over HTTPS, the meaningful part of the rule is usually the destination port and destination address, not the random high-numbered source port chosen for that individual connection. Good analysis depends on reading that pattern correctly.
Turning flow logs into usable insights with Athena
Flow logs become much more valuable when they are queryable. Athena gives teams a practical way to analyze VPC Flow Log data at scale — but to use it effectively, you first need to have your flow logs set up correctly.
VPC Flow Logs can be delivered to an S3 bucket in either the default space-delimited format or as Parquet. The Parquet format is significantly more efficient for Athena queries on large datasets and is worth configuring from the start if you are setting up a new pipeline.
Once the data is in S3, you define an external Athena table that maps to the flow log schema. The key columns for outbound egress analysis are:
- srcaddr — the source IP (your workload)
- dstaddr — the destination IP
- srcport — the ephemeral port used by your workload
- dstport — the service port on the destination (what you care about for egress rules)
- protocol — numeric protocol (6 = TCP, 17 = UDP)
- action — ACCEPT or REJECT
- flow_direction — available in v5+ logs; use egress to filter outbound traffic directly
A useful starting query for outbound hardening looks like this:
SELECT
srcaddr,
dstaddr,
dstport,
protocol,
COUNT(*) AS connection_count
FROM vpc_flow_logs
WHERE srcaddr = '10.0.1.45' -- your workload's private IP
AND action = 'ACCEPT'
AND flow_direction = 'egress' -- v5 logs only; remove if using v2
AND day BETWEEN '2024-01-01' AND '2024-01-31'
GROUP BY srcaddr, dstaddr, dstport, protocol
ORDER BY connection_count DESC
LIMIT 100;This produces a ranked view of the destinations and ports a workload contacts most frequently — exactly the evidence you need to write precise egress rules.
One important limitation to understand upfront: Flow Logs record IP addresses, not domain names. If your workload connects to a SaaS API like api.stripe.com or a container registry like registry-1.docker.io, the log shows only the resolved IP at that moment — which may change. This means IP-based egress rules alone are often not a complete solution for services that use dynamic or CDN-backed infrastructure. In those cases, egress hardening typically needs to be paired with a DNS-aware proxy or firewall, or managed through VPC endpoints where AWS services are involved.
From analysis to enforcement
The next step is translating observed traffic into policy.
Repeated, legitimate destinations can become candidate allow rules. For example, if a workload consistently connects to a known partner API over TCP 443, that pattern supports a narrow outbound rule. If multiple production workloads rely on the same service, you can standardize that rule and document it as a managed dependency.
At the same time, not every observed connection should become permanent policy.
Some traffic is temporary. Some of it may reflect troubleshooting, testing, outdated integrations, or one-off operational activity. That is why enforcement decisions should be based on both traffic evidence and system context. Logs show what happened. Engineering judgment determines what should continue to be allowed.
The objective is not perfect network minimization on day one.
The objective is progress: fewer unnecessary outbound paths, better visibility, stronger containment, and a policy set that is easier to explain and maintain.
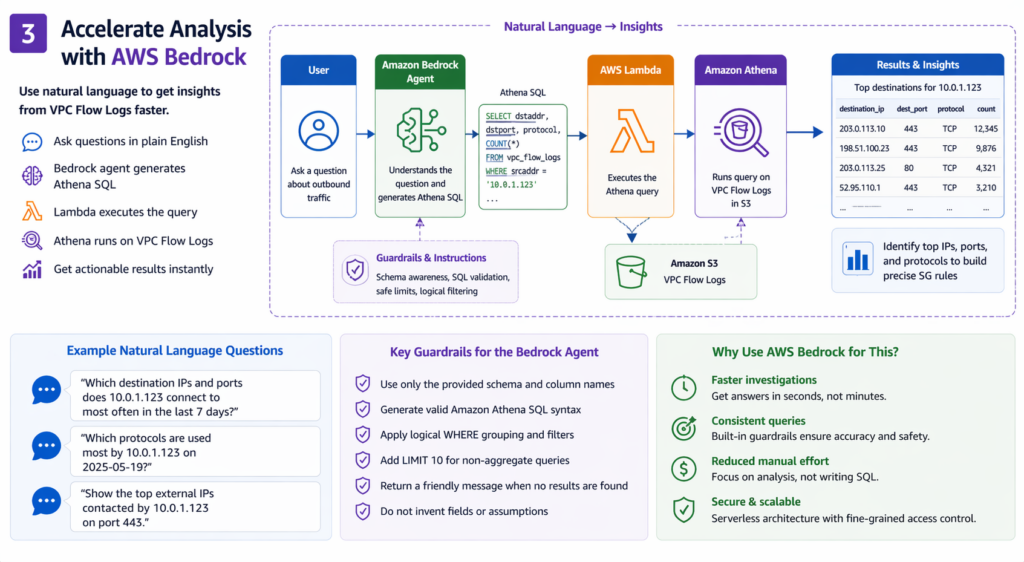
How AWS Bedrock can speed up the workflow
Writing Athena queries repeatedly for different workloads, time windows, and investigation questions takes time. Security teams usually know what they want to find — the top destination ports used by a workload, the most frequent outbound IPs in the last 30 days, protocol breakdowns per subnet — but translating those questions into clean, correct SQL each time creates friction.
A Bedrock-based agent can help here. In a common implementation, the user submits a question in plain language, the agent generates an Athena query, a Lambda function executes it, and the results come back as structured output. For repetitive investigation tasks, this can meaningfully reduce overhead.
But this pattern requires careful design, especially in a security context.
Large language models can generate plausible-looking SQL that contains invented column names, incorrect syntax, or logic errors that silently return wrong results. In a security investigation, a wrong result is worse than no result — it can create false confidence.
A robust implementation should include:
- Schema grounding: Provide the exact table schema in the agent’s system prompt or tool definition. Do not let the model infer column names.
- Query validation: Before execution, validate that generated SQL references only columns that exist in the schema and uses only permitted Athena syntax.
- Result limits: Always include a LIMIT clause by default to prevent runaway scans on large datasets.
- Read-only execution: The Lambda execution role should have read-only access to Athena and S3. It should never have permissions to modify flow log data or infrastructure.
- Human review before action: The agent’s output should be treated as a draft query to inspect, not a direct action to execute blindly.
Used well, Bedrock removes repetitive query-writing overhead so engineers can spend more time on interpretation and decision-making. The productivity benefit is real. But it only holds if the implementation is constrained enough that the model’s errors cannot produce misleading results or reach beyond the investigation scope.
Best practices for long-term outbound hardening
Outbound rule hardening works best when it becomes part of a broader cloud security discipline.
A few practices make a big difference over time.
First, treat outbound traffic as part of the attack surface, not just a routing detail. If an attacker cannot easily call out, many post-compromise actions become harder.
Second, use layered controls. Security Groups are important, but they are even more effective when combined with endpoint protection, network monitoring, WAF coverage where relevant, and strong IAM boundaries.
Third, use observed traffic data before making policy changes. Assumptions are rarely complete in real production environments.
Fourth, review rules regularly. Every exception should have a reason, and every reason should still be valid.
Finally, use AI to speed up analysis, not to bypass verification. Natural-language query generation is valuable, but production security decisions still need human review.
Final thoughts
For a long time, default outbound access has been treated as the easy option in AWS.
But easy is not the same as safe.
As cloud environments mature, outbound communication should become more intentional. Workloads do not need permission to talk to everything. They need permission to talk to the right things.
That is the difference between convenience-based configuration and least-privilege design.
VPC Flow Logs and Athena make that shift practical by turning network behavior into something measurable and queryable.
Bedrock can make the process faster by helping teams ask better questions in less time. Together, they support a more precise approach to outbound security: one built on evidence, not assumptions.
And that is the real goal of modern egress hardening. Not more rules for the sake of more rules, but better rules that match how systems actually work.
Need help reviewing AWS outbound traffic and designing least-privilege egress rules for production workloads? Talk to SupremeTech’s Cloud and DevOps team.
FAQs
Outbound rules control which connections a workload can initiate. If they are too broad, compromised systems may be able to reach unauthorized destinations, download payloads, or exfiltrate data.
Yes. AWS Security Groups are stateful, which means return traffic for an allowed connection is automatically permitted without needing a matching rule in the opposite direction.
Unrestricted outbound access makes it harder to enforce least privilege and harder to contain suspicious behavior after compromise. It increases exposure without adding real business value.
VPC Flow Logs help teams see where workloads are actually connecting. That makes it easier to identify required destinations and ports before replacing broad outbound access with tighter rules.
Athena helps analyze network traffic data from VPC Flow Logs, while AWS Bedrock can speed up investigation by helping teams turn natural-language questions into useful query patterns.
The goal is not to block everything blindly. It is to build evidence-based, least-privilege outbound rules that reflect real application behavior and reduce egress risk.