CI/CD Security Best Practices That Engineers and Decision-Makers Should Know
11/05/2026
3
CI/CD security best practices matter because the pipeline is no longer just an automation tool. It is one of the most powerful control points in modern software delivery. If attackers gain access to the CI/CD environment, they may be able to alter source code, steal secrets, tamper with build artifacts, or push compromised software into production.
This article focuses on the CI/CD security best practices engineers should know first. The goal is not to create a long checklist. It is to explain which controls matter most, why they matter, and how teams can reduce risk in a way that fits real delivery work. This article also listing what are the things about CI/CD that the decision-makers in the operation should always have in mind.
Why CI/CD Security Matters More Than Many Teams Expect

Many teams think about CI/CD mainly in terms of speed, automation, and release efficiency. That is understandable. Pipelines are often introduced to reduce manual work, standardize deployments, and help teams ship faster. The problem is that this can make the pipeline feel like plumbing instead of a security boundary.
In practice, a CI/CD pipeline usually has access to many of the most sensitive parts of the delivery environment. It may connect to source control, artifact repositories, cloud accounts, container registries, deployment credentials, signing processes, and production infrastructure. That means a pipeline compromise is rarely a small issue. It can affect code integrity, deployment trust, and downstream systems at the same time. CISA and NSA’s joint guidance on defending CI/CD environments highlights threats such as source code manipulation, credential theft, pipeline abuse, and malicious modification of dependencies and build outputs.
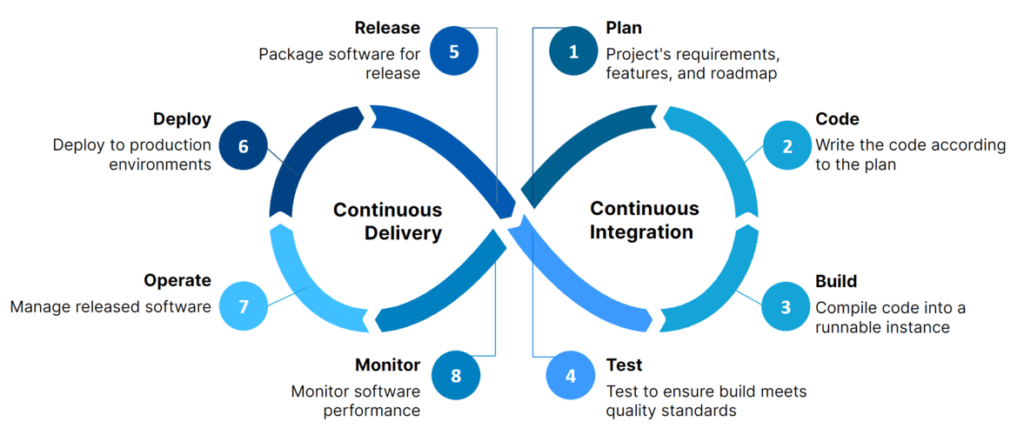
For engineers, the practical takeaway is simple. A pipeline should be treated as part of the production security boundary, not just as a convenience layer for deployment. When teams understand that, CI/CD security best practices become much easier to justify and prioritize.
Read related articles about DevSecOps:
- Zero-Exposure Data Mobility: AWS PrivateLink Cross-Account Database Migration Blueprint Using AWS DMS
- How to Harden AWS security group outbound rules with VPC Flow Logs, Athena, and AWS Bedrock
CI/CD Security Best Practices Engineers Should Prioritize First
The most effective CI/CD security best practices are the ones that protect the parts of the pipeline attackers actually target: access, secrets, build integrity, dependencies, artifacts, and deployment trust. CISA and NSA’s guidance, NIST SP 800-204D, OWASP’s CI/CD Security Cheat Sheet, and SLSA all point in that direction. They treat the pipeline as a critical security boundary, not just a release tool.
A practical way to organize the work is to focus on a smaller set of controls first.
| Best practice | What engineers should do in real life | Why it matters |
| Lock down pipeline access | Use least privilege for CI runners, repo access, cloud roles, and deployment credentials. Remove shared admin access. Require MFA and short-lived credentials where possible. | A pipeline often has access to source code, secrets, cloud resources, and production paths. Weak access control turns it into a high-value target. |
| Protect secrets properly | Move secrets out of code, config files, and pipeline variables where possible. Use a managed secrets system, rotate credentials, and avoid long-lived tokens in runners. | Stolen pipeline secrets can be enough to access cloud accounts, registries, or production systems. |
| Harden build runners and agents | Prefer ephemeral runners for untrusted jobs, isolate workloads, patch runner images, and avoid mixing sensitive and untrusted builds on the same executor. | Shared or long-lived runners can leak credentials, artifacts, or state between jobs. |
| Verify code and dependency integrity | Scan dependencies, pin versions, review third-party actions or plugins, and control where packages can be pulled from. | Many pipeline attacks move through compromised dependencies or build-time components rather than source code alone. |
| Secure artifacts and releases | Sign artifacts, control who can publish them, store provenance when possible, and verify what gets promoted between stages. | Teams need confidence that what is deployed is exactly what was built and approved. |
| Enforce policy in the pipeline | Add automated checks for IaC, secrets, dependency risk, container issues, and branch protections. Use policy-as-code where possible. | Security only scales in CI/CD when controls are automatic, consistent, and hard to bypass. |
| Separate environments and trust boundaries | Keep development, staging, and production credentials and deployment paths clearly separated. Avoid broad cross-environment trust. | A weak lower environment should not become an easy path into production. |
| Log and monitor pipeline activity | Record job execution, privileged changes, token use, artifact publication, and unusual pipeline behavior. Alert on sensitive actions. | Detection matters because pipeline abuse is often quiet and may look like normal automation at first. |
1. Lock down who and what can use the pipeline
A CI/CD system should not have broad standing access by default. In real environments, that means engineers should review repo permissions, pipeline service accounts, runner permissions, deployment roles, and approval paths. Build systems often end up with much more access than they actually need.
This is one of the clearest lessons from the CISA and NSA guidance. Their recommendations emphasize restricting access, hardening identity controls, and reducing the paths an attacker can use to manipulate builds or deployments.
2. Treat secrets as one of the highest-risk parts of the pipeline
In practice, many CI/CD compromises become serious because of secrets, not because of the pipeline engine alone. Hardcoded credentials, long-lived tokens, exposed environment variables, and over-permissioned cloud keys all create easy paths for abuse.
OWASP’s cheat sheet puts strong emphasis on secret management, least privilege, and avoiding credential exposure in jobs and pipeline configuration. The practical rule is simple: if a pipeline secret can unlock production access, it deserves the same protection as any other privileged credential.
3. Protect the integrity of what gets built and released
Securing the pipeline is not only about blocking access. It is also about making sure the output can be trusted. That is where artifact integrity, provenance, and release trust become important.
NIST SP 800-204D and SLSA are especially useful here because they frame CI/CD security as part of software supply chain integrity. In real engineering terms, that means teams should care about signed artifacts, trusted build paths, controlled promotion between environments, and evidence that the build came from the expected source and process.
4. Put security checks into the delivery flow, not after it
If pipeline security depends on manual review at the end, it usually does not scale. Teams move too fast, and reviewers become bottlenecks. A better model is to place automated checks inside the normal delivery path.
That can include:
- branch protection and review requirements
- secret scanning
- dependency and artifact scanning
- infrastructure-as-code checks
- policy enforcement before deploy
- approval requirements for sensitive releases
This is where CI/CD security becomes practical. The goal is not to stop every build. It is to make insecure changes harder to ship silently.
5. Design the pipeline for containment, not just speed
Many teams optimize pipelines heavily for throughput, but do less work on isolation. In real life, that can create risk when untrusted pull requests, third-party actions, or multiple workloads share the same runners, caches, or credentials.
A stronger design uses isolation deliberately:
- separate trusted from untrusted jobs
- avoid reusing sensitive runner state
- isolate production deployment paths
- reduce shared credentials across projects
- contain blast radius if one pipeline job is compromised
That is often the difference between a pipeline issue and a full delivery-chain incident.
What Decision-Makers Should Know About Managing CI/CD Security

Leaders do not need to manage every pipeline check themselves. But they do need to understand that CI/CD security is not only an engineering detail. It affects release trust, cloud access, software integrity, and the speed at which one mistake can spread across the delivery chain. CISA and NSA treat CI/CD as a high-value target for exactly that reason.
The leadership job is usually simpler than the technical work. It is about making sure ownership, priorities, and decision paths are clear.
What leaders should pay attention to
| Area | What leaders should check | Why it matters |
| Ownership | Is it clear who owns pipeline access, secrets, artifact integrity, and remediation? | Shared responsibility fails when no one owns the risky parts. |
| Access | Do CI/CD systems have more privilege than they need? | Over-permissioned pipelines create a direct path to code, cloud, and production. |
| Secrets | Are secrets short-lived, rotated, and kept out of code and logs? | Secret exposure is one of the fastest ways a pipeline issue becomes a wider incident. |
| Build trust | Can the team prove what was built, how it was built, and what was deployed? | Software supply chain guidance such as SLSA and NIST SP 800-204D puts strong emphasis on build integrity and provenance. |
| Release friction | Are security checks helping teams ship safely, or just creating late-stage blockers? | A security model that only blocks releases usually gets bypassed over time. |
| Containment | If one repo, runner, or token is compromised, how far can the damage spread? | Good CI/CD security limits blast radius instead of assuming nothing will fail. |
Practical questions a CEO, CTO, or engineering leader can ask
| Question | What it reveals |
| Who can change pipeline configuration or deployment logic? | Whether control over the delivery chain is too broad |
| Which pipeline credentials can reach production? | Whether the blast radius is larger than expected |
| What security findings block releases today? | Whether controls are meaningful or mostly cosmetic |
| How do we know an artifact in production came from a trusted build? | Whether build integrity is actually being managed |
| Where do critical pipeline issues stay open the longest? | Whether ownership and escalation are working |
The main point is simple: leaders do not need to know every CI/CD tool in detail. They do need to know whether the organization can trust its delivery chain, whether responsibility is clear, and whether pipeline security is supporting delivery or quietly putting it at risk.
Why the Right Technology Partner Matters
CI/CD security is easy to oversimplify. On the surface, it can look like a matter of adding a few scanners, tightening access, and improving secrets management. In real delivery environments, the harder part is making those controls work inside day-to-day engineering without turning the pipeline into a bottleneck.
That is where the right technology partner can make a real difference. A strong partner does more than add security tools into the delivery flow. They help design a practical model for secure CI/CD by connecting pipeline hardening, cloud access control, build integrity, and remediation workflows in a way that fits how the business actually ships software.
SupremeTech can support organizations through system modernization, custom digital product development, enterprise integration, and offshore development support for teams that need more structured execution across complex engineering environments. In CI/CD security work, those capabilities matter because secure delivery is not only about the pipeline itself. It also depends on how well security controls fit the broader architecture, cloud environment, and development model of the business.
Conclusion
CI/CD security best practices matter because the pipeline is not just a delivery tool. It is part of the software trust boundary. If access is too broad, secrets are poorly managed, artifacts are not trustworthy, or pipeline controls are easy to bypass, the risks can spread far beyond one build job or one release.
That is why secure CI/CD should be treated as part of the wider software delivery model, not as a set of extra checks added at the end. The most effective teams focus on a smaller group of high-value controls first: access, secrets, runner hardening, artifact integrity, policy enforcement, and containment. When those areas are managed well, the pipeline becomes easier to trust and easier to scale.
For engineers and decision-makers alike, the practical takeaway is simple. Good CI/CD security is not about slowing releases down. It is about making sure the delivery chain stays reliable, defensible, and sustainable as the business grows.
CI/CD security best practices are the controls and engineering practices used to protect source code, secrets, build systems, artifacts, and deployment workflows across the software delivery pipeline.
CI/CD security is important because the pipeline often has access to source repositories, cloud credentials, deployment paths, and production environments. If it is compromised, attackers may be able to tamper with code or push malicious software into production.
A practical starting point includes pipeline access, secrets management, runner hardening, dependency integrity, artifact trust, policy enforcement, and environment separation.
A common mistake is treating the pipeline as trusted by default and giving runners, service accounts, or deployment jobs more access than they actually need.
It matters because teams need confidence that what is deployed is exactly what was built, reviewed, and approved. Without that, software supply chain risk becomes much harder to control.
Leaders should focus on ownership, access levels, secret handling, build trust, release friction, and whether the delivery chain can contain damage if one part is compromised.