How to Ensure Data Security When Outsourcing?
24/04/2023
1.97k
Table of Contents
As ransomware attacks and data leaks increase, data security when outsourcing is a major concern. Therefore, businesses must adopt the highest security standards to protect themselves, their employees, partners, and clients. In this blog, we will share the most common data risks when outsourcing and solutions. Check it out!
What are the data risks when outsourcing?
Before choosing whether outsourcing is right for your company, it is critical to understand the common data risks. Here are the top 4 risks when outsourcing:
Unauthorized access
When technology is outsourced, monitoring and managing might be more challenging. The more privileged credentials are cultivated, the more unauthorized access and data breaches increase. There is a risk that unauthorized individuals will gain access to your private information if the outsourcing provider lacks adequate security measures. This may result in data breaches or identity fraud.
Data theft and breaches
According to the Cybersecurity Outlook 2022, indirect cyberattacks—successful breaches that enter businesses through third parties—have grown to 61% from 44% in recent years. One reason for this is that many businesses lack the necessary controls to successfully offboard their partners.
Threat actors can abuse the data taken to perform various malicious activities, including fraud, account abuse, identity theft, and account takeover attacks. Due diligence and ongoing vulnerability monitoring throughout the vendor lifecycle will help to minimize that risk. A defense-in-depth approach to restrict unauthorized third-party access to an organization’s network is essential to preventing adversaries from obtaining privilege escalation.

Loss of Data Control
When a company distributes responsibility for developing and operating its information system to another outsourcing company, it may lose control over the data.
If the vendor is the only option for running and developing the company’s information system, the company must accept any technology the vendor provides. This dependency can result in higher expenses or losing control over their data.
Therefore, you should select the correct partner to handle data as a sensitive issue. Since procedures that aren’t carried out in-house are inherently less controllable, a company should be able to conduct audits on its outsourcing partners as required.
⇒ You might be interest in: In house vs outsourcing application development: Which is best?
Regulatory Compliance Violations
This happens when third-party vendors break governmental laws, industry rules, or internal company procedures. As a result, your companies could be subject to severe monetary penalties.
Your company, for example, must ensure that the third-party suppliers comply with the SOC2 auditing standard. SOC2 aims to make sure that third parties safeguard their customers’ data from unauthorized access. Organizations must ensure that third parties follow privacy and security legislation, such as the European Union’s General Data Protection Regulation (GDPR) and the California Privacy Rights Act (CPRA).
How to Ensure Data Security When Outsourcing
Here is a list of best practices recommended to ensure data security when outsourcing:
Sign a Comprehensive Contract
A Comprehensive contract allows parties to restrict their activities to the intended purposes. Such agreements, once signed, serve as proof of their intentions and show their ultimate understanding of the transaction.
When a company outsources, it is critical for them to make written agreements with the outsource provider outlining how their data will be used, shared, or transferred for the purposes specified in the contract. This restricts third-party access to their data and subjects them to penalties in the event of a breach, enabling businesses to preserve confidential information even when it is not in their control.

Implement Data Security Measures
As technologies advance, the demand for more sophisticated data security solutions increases. Before giving your outsourcing partner access to sensitive data, ensure they use cutting-edge software tools and protection methods. This step plays an important role in ensuring sufficient data security when outsourcing.
Check with the ITO provider you are partnering with that has the required tools to prevent viruses and spyware and an action plan in the event of a cyber attack. Regular penetration tests are required to discover security loopholes.
Train Employees
Training data security is a critical step that everyone must participate in, particularly those employees who are actively handling and processing customer data. An excellent company will:
- Provide ongoing training on data security
- Keep up with compliance and regulatory procedures and ensure employees are aware of them
- Encourage employees to disclose security concerns and incidents
- Audit employee handling of customer data on a frequent basis
When workers are in a rush, keeping up with data security and compliance measures can fall by the wayside. As a result, conducting regular training and audits guarantees that workers are following compliance procedures.
Regularly Monitor Data Security
A company’s in-house IT and data security staff should periodically monitor and review the most recent data security threats. Employees in-house can be trained to examine and check the progress of any outsourced work. They can also be prepared to be cautious of potential data breaches or suspicious behavior.
Conclusion
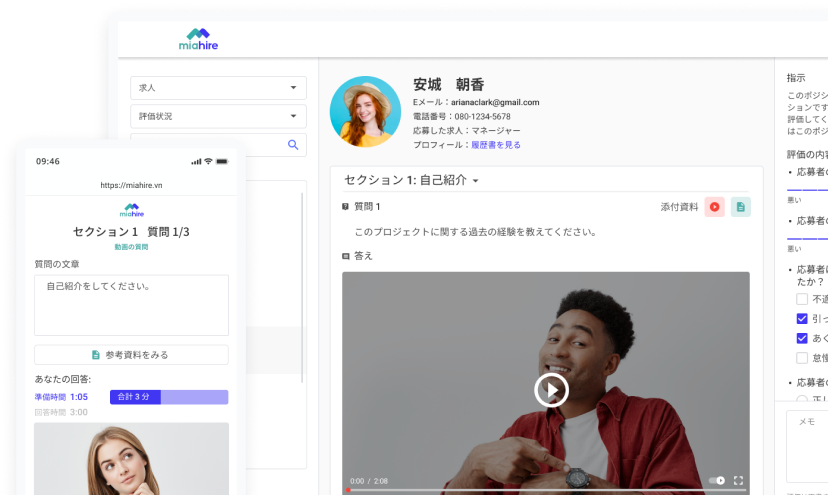
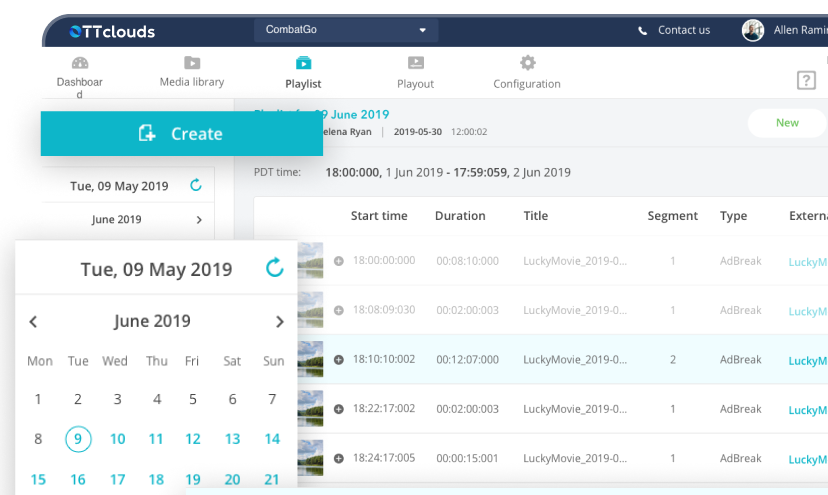
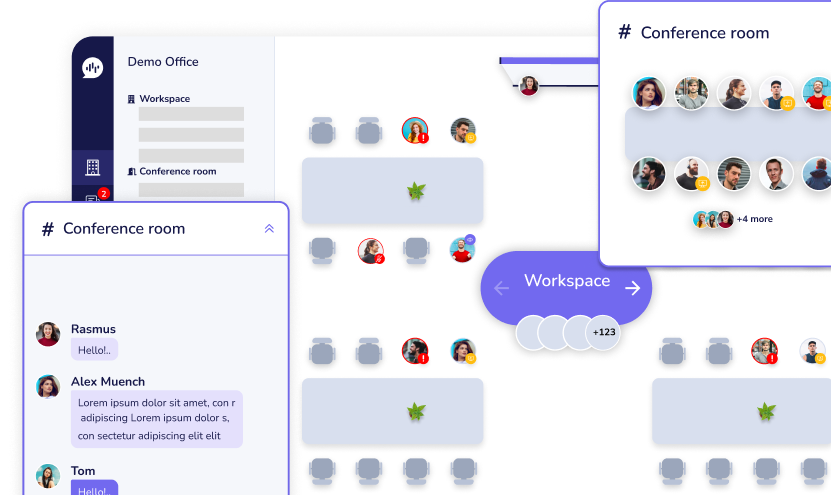
At SupremeTech, we frequently help clients optimize internal data security when outsourcing, as well as provide a variety of service areas, such as web and mobile development. Our outsourcing services are implementing a unique data-driven approach within our high-performance teams and highly engaged culture. To experience the advantages and achieve data security in outsourcing,
Visit our website today!
Related Blog